A brand new examine of built-in growth environments (IDEs) like Microsoft Visible Studio Code, Visible Studio, IntelliJ IDEA, and Cursor has revealed weaknesses in how they deal with the extension verification course of, finally enabling attackers to execute malicious code on developer machines.
“We found that flawed verification checks in Visible Studio Code enable publishers so as to add performance to extensions whereas sustaining the verified icon,” OX Safety researchers Nir Zadok and Moshe Siman Tov Bustan stated in a report shared with The Hacker Information. “This leads to the potential for malicious extensions to seem verified and authorised, making a false sense of belief.”
Particularly, the evaluation discovered that Visible Studio Code sends an HTTP POST request to the area “market.visualstudio[.]com” to find out if an extension is verified or in any other case.
The exploitation methodology primarily entails making a malicious extension with the identical verifiable values as an already verified extension, comparable to that of Microsoft, and bypassing belief checks.
In consequence, it permits rogue extensions to seem verified to unsuspecting builders, whereas additionally containing code able to executing working system instructions.
From a safety standpoint, it is a basic case of extension sideloading abuse, the place unhealthy actors distribute plugins exterior the official market. With out correct code signing enforcement or trusted writer verification, even legitimate-looking extensions can cover harmful scripts.
For attackers, this opens up a low-barrier entry level to attain distant code execution—a danger that is particularly severe in growth environments the place delicate credentials and supply code are sometimes accessible.
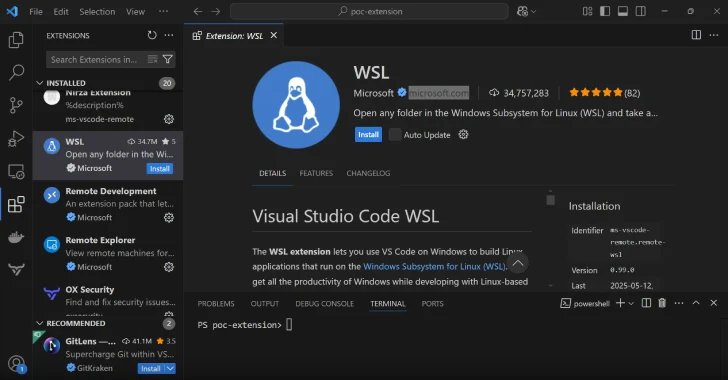
In a proof-of-concept (PoC) demonstrated by the cybersecurity firm, the extension was configured to open the Calculator app on a Home windows machine, thereby highlighting its capacity to execute instructions on the underlying host.
By figuring out the values utilized in verification requests and modifying them, it was discovered that it is attainable to create a VSIX bundle file such that it causes the malicious extension to seem legit.
OX Safety stated it was capable of reproduce the flaw throughout different IDEs like IntelliJ IDEA and Cursor by modifying the values used for verification with out making them lose their verified standing.
In response to accountable disclosures, Microsoft stated the conduct is by design and that the adjustments will stop the VSIX extension from being revealed to the Market owing to extension signature verification that is enabled by default throughout all platforms.
Nevertheless, the cybersecurity firm discovered the flaw to be exploitable as not too long ago as June 29, 2025. The Hacker Information has reached out to Microsoft for remark, and we are going to replace the story if we hear again.
The findings as soon as once more present that relying solely on the verified image of extensions may be dangerous, as attackers can trick builders into working malicious code with out their information. To mitigate such dangers, it is suggested to put in extensions straight from official marketplaces versus utilizing VSIX extension recordsdata shared on-line.
“The power to inject malicious code into extensions, bundle them as VSIX/ZIP recordsdata, and set up them whereas sustaining the verified symbols throughout a number of main growth platforms poses a severe danger,” the researchers stated. “This vulnerability notably impacts builders who set up extensions from on-line assets comparable to GitHub.”