Cybersecurity researchers have found a bypass for a now-patched safety vulnerability within the NVIDIA Container Toolkit that might be exploited to interrupt out of a container’s isolation protections and acquire full entry to the underlying host.
The brand new vulnerability is being tracked as CVE-2025-23359 (CVSS rating: 8.3). It impacts the next variations –
- NVIDIA Container Toolkit (All variations as much as and together with 1.17.3) – Mounted in model 1.17.4
- NVIDIA GPU Operator (All variations as much as and together with 24.9.1) – Mounted in model 24.9.2
“NVIDIA Container Toolkit for Linux comprises a Time-of-Verify Time-of-Use (TOCTOU) vulnerability when used with default configuration, the place a crafted container picture might acquire entry to the host file system,” the corporate stated in an advisory on Tuesday.
“A profitable exploit of this vulnerability may result in code execution, denial of service, escalation of privileges, data disclosure, and knowledge tampering.”
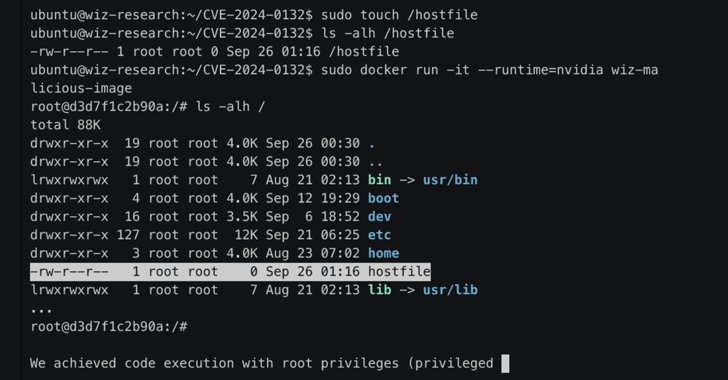
Cloud safety agency Wiz, which shared extra technical specifics of the flaw, stated it is a bypass for an additional vulnerability (CVE-2024-0132, CVSS rating: 9.0) that was addressed by NVIDIA in September 2024.
In a nutshell, the vulnerability allows unhealthy actors to mount the host’s root file system right into a container, granting them unfettered entry to all information. Moreover, the entry will be leveraged to launch privileged containers and obtain full host compromise through the runtime Unix socket.
Wiz researchers safety researchers Shir Tamari, Ronen Shustin, and Andres Riancho stated their supply code evaluation of the container toolkit discovered that the file paths used throughout mount operations might be manipulated utilizing a symbolic hyperlink such that it makes it potential to mount from exterior the container (i.e., the foundation listing) right into a path inside “/usr/lib64.”
Whereas the entry to the host file system afforded by the container escape is read-only, this limitation will be circumvented by interacting with the Unix sockets to spawn new privileged containers and acquire unrestricted entry to the file system.
“This elevated stage of entry additionally allowed us to observe community site visitors, debug energetic processes, and carry out a variety of different host-level operations,” the researchers stated.
Apart from updating to the most recent model, customers of the NVIDIA Container Toolkit are really helpful to not disable the “–no-cntlibs” flag in manufacturing environments.