Taiwanese entities in manufacturing, healthcare, and knowledge expertise sectors have grow to be the goal of a brand new marketing campaign distributing the SmokeLoader malware.
“SmokeLoader is well-known for its versatility and superior evasion methods, and its modular design permits it to carry out a variety of assaults,” Fortinet FortiGuard Labs stated in a report shared with The Hacker Information.
“Whereas SmokeLoader primarily serves as a downloader to ship different malware, on this case, it carries out the assault itself by downloading plugins from its [command-and-control] server.”
SmokeLoader, a malware downloader first marketed in cybercrime boards in 2011, is mainly designed to execute secondary payloads. Moreover, it possesses the aptitude to obtain extra modules that increase its personal performance to steal information, launch distributed denial-of-service (DDoS) assaults, and mine cryptocurrency.
“SmokeLoader detects evaluation environments, generates pretend community visitors, and obfuscates code to evade detection and hinder evaluation,” an intensive evaluation of the malware by Zscaler ThreatLabz famous.
“The builders of this malware household have constantly enhanced its capabilities by introducing new options and using obfuscation methods to impede evaluation efforts.”
SmokeLoader exercise suffered a significant decline following Operation Endgame, a Europol-led effort that took down infrastructure tied to a number of malware households similar to IcedID, SystemBC, PikaBot, SmokeLoader, Bumblebee, and TrickBot in late Might 2024.
As many as 1,000 C2 domains linked to SmokeLoader have been dismantled, and greater than 50,000 infections have been remotely cleaned. That having stated, the malware continues for use by risk teams to distribute payloads by way of new C2 infrastructure.

This, per Zscaler, is essentially because of quite a few cracked variations publicly obtainable on the web.
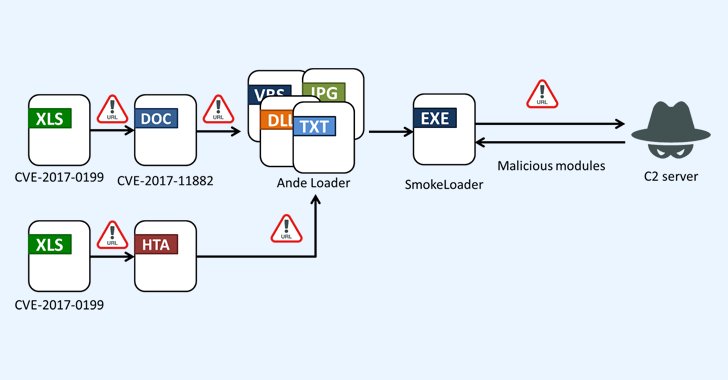
The start line of the newest assault chain found by FortiGuard Labs is a phishing electronic mail containing a Microsoft Excel attachment that, when launched, exploits years-old safety flaws (e.g., CVE-2017-0199 and CVE-2017-11882) to drop a malware loader known as Ande Loader, which is then used to deploy SmokeLoader on the compromised host.
SmokeLoader consists of two parts: a stager and a principal module. Whereas the stager’s objective is to decrypt, decompress, and inject the principle module into an explorer.exe course of, the principle module is accountable for establishing persistence, speaking with the C2 infrastructure, and processing instructions.
The malware helps a number of plugins that may steal login and FTP credentials, electronic mail addresses, cookies, and different info from net browsers, Outlook, Thunderbird, FileZilla, and WinSCP.
“SmokeLoader performs its assault with its plugins as an alternative of downloading a accomplished file for the ultimate stage,” Fortinet stated. “This reveals the pliability of SmokeLoader and emphasizes that analysts should be cautious even when taking a look at well-known malware like this.”